Okta OIDC
Supported Features
Single Sign-On (OpenID Connect) Service Provider (SP)-Initiated Authentication (SSO) Flow - this authentication flow occurs when the user attempts to log in to the application from Convrs.
Role management features are not supported. Users and their Convrs roles will still need to be managed from the Convrs Agent Management page.
Requirements
- Be on a Convrs Enterprise price tier.
- Admin access to your Okta organization account.
- Admin access to your Convrs account.
- Convrs agent emails exactly match their Okta accounts
Configuration Steps
- In Okta, Go to Applications → Browse App Catalog, and search and add Convrs
- Assign the users or groups that should be able to log into Convrs.
Gather Information from Okta
Three pieces of information are needed from Okta, the Client ID, Client Secret, and the issuer URL.
- Go to the Convrs App in Okta, then in the sign-on tab and take a copy of the Client ID and the Client Secret.
- There should be a section that has a link titled OpenID Provider Metadata. Click this link. In the JSON document shown, look for a key titled “issuer” and copy the URL value.
- Contact Convrs support and provide the Client ID, Client Secret, and Okta Issuer URL.
- We will provide you with an AccountID that you populate within the AccountID field in Okta. Save your changes.
Configure Convrs
Once we have confirmed that Okta has been configured, you can now configure Convrs:
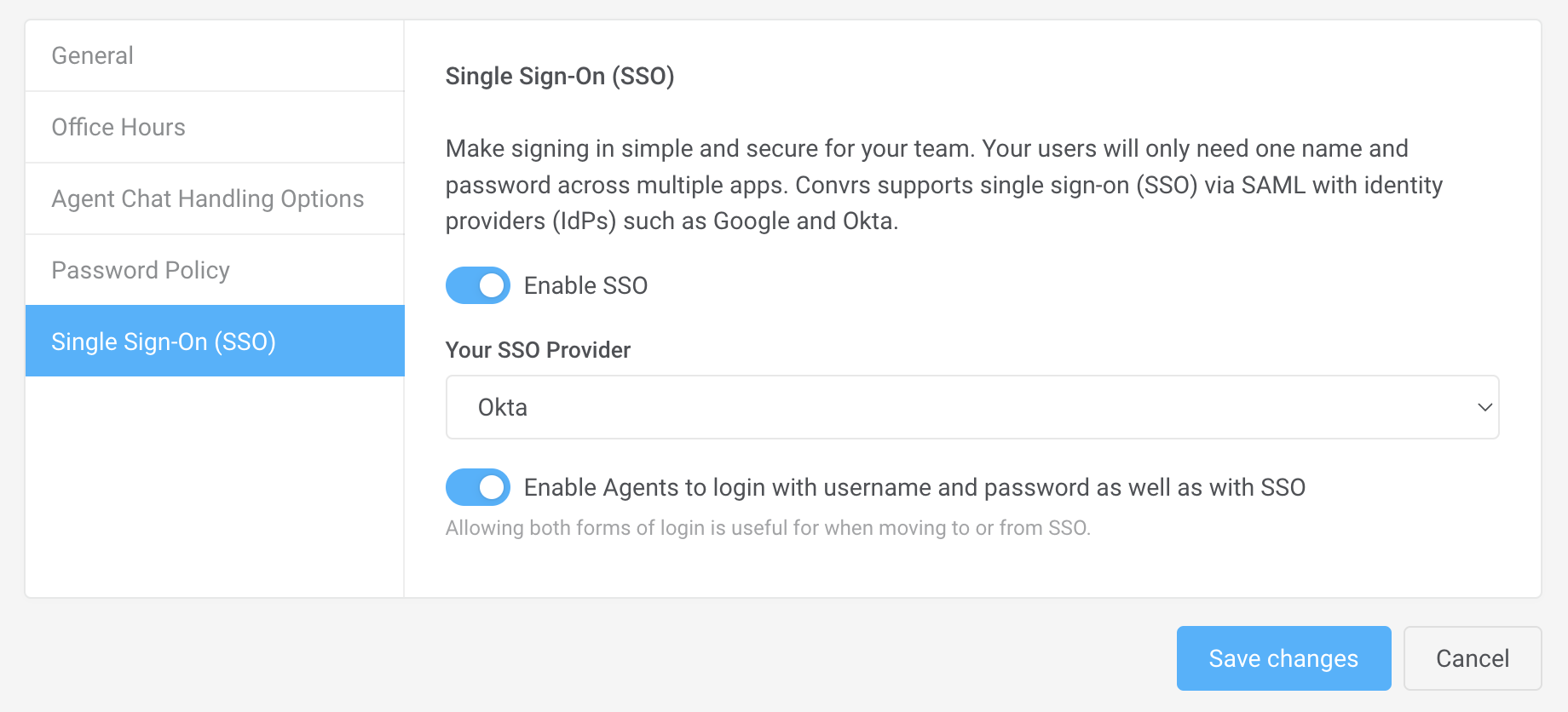
- Navigate to the Single Sign-On tab within the Convrs admin panel (Administration→ Organization Profile). Then enable SSO. Then select Okta as your SSO provider. If you are migrating to Okta, you may also wish to turn on Enable Agents to log in with username and password as well as with SSO. Once you are happy that your agents can log in via Okta, you can turn this off.
Notes
Once the configuration steps have been completed, go to the Convrs login page, press Sign in With Okta, and enter your email address. Then press the Login button and follow the Okta login process.